Organizations need critical system protection to keep their legacy systems and embedded devices safe from sophisticated cyber threats. Symantec Critical System Protection (SCSP) works as a lightweight behavioral hardening engine. It adds defensive layers at the kernel level to prevent unhygienic operations on IoT devices and machines.
SCSP helps organizations protect their heterogeneous server environments and data proactively. It combines host-based intrusion detection, intrusion prevention, and least privilege access control. Many users want to learn about SCSP’s security capabilities beyond its reliable framework. The system has managed to keep a clean vulnerability record since 2020, with zero published security vulnerabilities. This impressive track record tells only part of the story. The Critical Systems Protection program goes beyond software solutions. Specially trained agents work to identify, assess, and mitigate cyber risks as part of protective operations.
This piece gets into the hidden vulnerabilities, limitations, and blind spots that security experts rarely discuss about Symantec Critical System Protection. The insights are a great way to get knowledge for organizations that rely on this technology to secure their critical infrastructure.
The Real Scope of Symantec Critical System Protection
SCSP (Symantec Critical System Protection) stands out as a specialized enterprise security solution. It focuses on infrastructure protection rather than endpoint detection. A deep dive into its actual implementation scope reveals more than what marketing materials suggest.
What is Symantec Critical System Protection and Who Uses It?
SCSP works as a policy-based host security solution. It combines intrusion prevention and detection features that work with multiple platforms and applications. The system runs as a lightweight behavioral hardening engine. Its design protects legacy systems, end-of-life (EOL) systems, and embedded devices by adding defensive layers at the kernel level. The solution has:
- Proactive attack prevention through least privilege containment approaches
- Immediate file integrity monitoring to audit compliance
- Granular change detection of registry values, file contents, and attributes
- Operating system and application log monitoring
The United States houses 64% of Symantec Critical System Protection customers, while the UK has 6%. IT and Services lead the industry usage at 29%, with Financial Services following at 7%. Big names using SCSP include EPAM Systems, Infosys, General Dynamics Information Technology, Zensar Technologies, and Booz Allen Hamilton.
Market data shows that 57% of SCSP customers are enterprises with over 1000 employees. Medium-sized companies make up 22%, while small businesses with fewer than 50 employees account for 15%.
Kernel-Level Hardening vs Application-Level Security
SCSP’s strength comes from its kernel-level hardening capabilities. This approach differs substantially from standard application-level security measures. Kernel-level protection lets SCSP shield operating systems, applications, and services by setting acceptable behaviors for each function.
The in-kernel reference monitor contains operating system and application processes in a sandbox. This setup allows detailed access control across:
- Network communications
- File systems and registry
- Process-to-process memory access
- System calls
- Application and child process launches
Kernel-level protection guards better against day-zero attacks than application-level security. SCSP has specific buffer overflow protection for Microsoft Windows and exploit prevention techniques that block unknown exploits.
But this approach comes with trade-offs. Kernel-level security needs deeper system integration, which can make implementation more complex. Application-level security usually offers better control over specific program behaviors, while kernel-level hardening protects the system more broadly.
Limitations in Legacy and Embedded Device Coverage
SCSP markets itself as a solution for legacy systems and embedded devices, but it has some coverage limits. The Web console interface shows these constraints – users “cannot edit legacy CSP and DCS policies” through this interface. Administrators must use the management console for certain tasks, which creates workflow issues.
Embedded devices pose unique challenges for SCSP. The UK government’s cybersecurity arm RITICS points out that OT and ICS networks are fundamentally different from traditional IT networks. IT security prioritizes data confidentiality, while OT security focuses on device availability and integrity.
SCSP’s incident response approach might not fit embedded device needs. RITICS explains: “ICS/OT systems and networks are typically sensitive to availability and integrity requirements, requiring the Incident Response procedures to consider how systems can be interacted with for forensic collection”.
Starting with version 7.2, SCSP became available in a single platform-agnostic SKU that works with both devices and controllers. Earlier versions had separate SKUs for IoT devices and controlling devices, which highlighted the different protection needs of these environments.
Undocumented Vulnerabilities in SCSP Deployments
Symantec Critical System Protection’s security facade looks resilient, but it hides several critical vulnerabilities that few people discuss openly. These security flaws put organizations at risk of breaches that could disrupt their critical infrastructure.
Authentication Bypass in SCSP 8.0 (CVE-2019-18374)
Symantec Critical System Protection versions 8.0, 8.0 HF1, and 8.0 MP1 had a severe authentication bypass vulnerability that scored CVSS 3.1 score of 9.8 (Critical). This vulnerability let threat actors bypass authentication controls completely without any prior authentication or user interaction. The “Critical” risk factor showed how this vulnerability could severely affect system confidentiality, integrity, and availability. Symantec ended up fixing this issue by releasing version 8.0 MP1 HF1.
SQL Injection in Management Server (CVE-2015-8157)
The Management Server component across multiple Symantec products had an SQL injection vulnerability with a CVSS 3.1 score of 8.8 (High). This flaw showed up in several products including Critical System Protection before 5.2.9 MP6 and let remote authenticated users run arbitrary SQL commands. Attackers who exploited this could add themselves as server administrators. The vulnerability’s CVSS vector CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H showed how seriously it could disrupt system security.
Directory Traversal in SES:CSP 1.0.x (CVE-2015-8799)
The Management Server in multiple Symantec products, including Embedded Security: Critical System Protection (SES:CSP) 1.0.x before 1.0 MP5, had a directory traversal vulnerability. This vulnerability got a CVSS 2.0 score of 7.1 (High). Remote authenticated users could write update-package data to any agent location through unspecified vectors. Proper exploitation of this vulnerability could lead to code execution and bypass SCSP’s core security protections.
Cross-Site Scripting in ajaxswing WebUI (CVE-2014-9224)
The ajaxswing webui in the Management Console server had a cross-site scripting (XSS) vulnerability that affected Symantec Critical System Protection 5.2.9 through MP6. Despite its lower CVSS 2.0 severity score of 3.5 (Low), this vulnerability allowed remote authenticated users to inject web scripts or HTML through unspecified vectors. Attackers could steal user sessions and access the admin interface without authorization. This vulnerability raised concerns because it affected the main interface administrators use to configure their critical system protection policies.
These vulnerabilities show why organizations must keep their critical system protection deployments updated. Many organizations might still run older, vulnerable versions without knowing the security risks.
Blind Spots in Cyber-Physical Security Integration
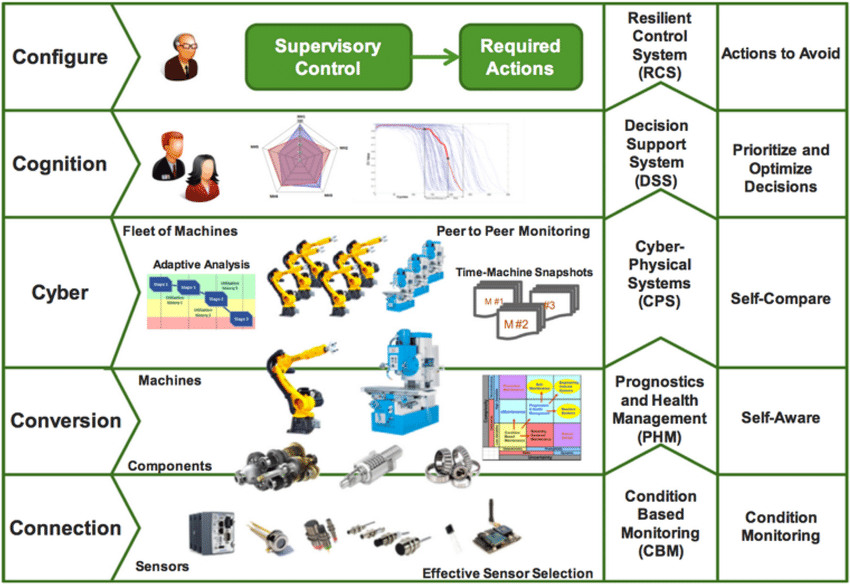
The integration of cyber and physical systems creates unique challenges that go beyond documented vulnerabilities in Symantec Critical System Protection. Security teams often miss these blind spots even in deployments that appear secure.
Failure Points in Protectee Site Network Assessments
Network assessments fail to address the most important vulnerabilities in cyber-physical systems integration. Organizations cannot see what connects to their network, which creates major security gaps. This blind spot reduces the effectiveness of firewalls and advanced threat protection.
Securing networks helps protect businesses from cyber attacks. However, assessment methods miss key failure points:
- Poor reviews of access management and network enforcement of trust
- Limited analysis of vulnerability detection capabilities
- Poor visibility into connected devices in OT environments
IT and OT systems meet in ways that bring substantial cybersecurity challenges. This expands the attack surface for cyber incidents that could disrupt critical missions. High-value systems become easier targets for hacking groups and nation-state adversaries.
Unsecured Control Systems in NSSE Deployments
National Security Special Events (NSSE) deployments face special risks from unsecured control systems. Many legacy OT systems were built to stay isolated or air-gapped, with no plans to connect to IT networks. These systems become vulnerable to multiple attack paths once connected.
NSSE deployments often use routable public-facing IP addresses instead of private ones. This makes these addresses available worldwide. Symantec Critical System Protection monitoring edition cannot properly address these additional attack vectors.
Legacy OT systems lack proper input validation. This makes them vulnerable to executing arbitrary code. Memory corruption, buffer overflows, and directory traversals can happen as a result.
Lack of Real-Time Monitoring in SCSP Monitoring Edition
Symantec Critical System Protection’s monitoring capabilities have major limitations. SCSP provides up-to-the-minute data analysis tools to view events at the management server. However, these tools focus on troubleshooting rather than detailed security monitoring.
SCSP’s monitoring tools show newest events first but lack advanced threat detection features. The tools depend heavily on user-defined filter rules and priorities. This creates uneven security visibility across deployments.
SCSP monitoring architecture needs manual setup of multiple real-time monitors for detailed visibility. This approach increases work overhead and creates potential monitoring gaps compared to modern security solutions. Users must share monitoring accounts like the default symadmin. This creates extra security risks when the core team needs access.
Tooling Gaps and Monitoring Limitations
Digital forensic tools linked to Symantec Critical System Protection show major limitations that affect security in critical environments. These weaknesses create vulnerabilities in systems that look secure on the surface.
Tamizar Forensics Tool: Capabilities and Shortcomings
The Tamizar forensics tool shows reliability and validation problems like many other digital forensic investigation tools. User authentication poses serious security risks, especially during urgent incident responses. Evidence collected through Tamizar lacks credibility due to chain of custody issues. These limitations create problems for organizations that rely on Symantec Critical System Protection to secure their critical infrastructure.
Kaleidoscope and Compass: Limited Threat Detection Scope
Kaleidoscope is another tool with major detection limitations. We focused mainly on mobile fraud detection instead of providing detailed infrastructure protection. The tool targets Android ad fraud operations hidden behind legitimate-looking applications. Kaleidoscope doesn’t deal very well with:
- Sophisticated threats that change structure to avoid detection
- Non-advertising based attacks
- Encrypted communication channels
Kaleidoscope’s detection methods focus only on app cloning and SDK rebranding techniques. Compass shows similar restrictions with limited detection scope, which ended up leaving critical gaps in protection.
Absence of AI-Driven Anomaly Detection in SCSP
The most concerning issue is that Symantec Critical System Protection lacks built-in AI-driven anomaly detection – a standard feature in modern security tools. This creates blind spots in finding unknown threats and zero-day exploits. Tools show performance issues under heavy loads, exactly when anomaly detection becomes vital.
Organizations using SCSP face these challenges:
- Limited live anomaly identification
- Poor detection of evolving threats
- Heavy reliance on signature-based detection
These gaps in tools and monitoring create systemic vulnerabilities beyond those listed in traditional CVE entries. This exposes critical systems to sophisticated attacks.
Partnerships and Their Hidden Trade-offs
Security partnerships improve Symantec Critical System Protection’s capabilities but come with complex trade-offs that rarely get examined. Organizations should carefully assess these hidden costs before they deploy SCSP in their critical systems.
CERT and Sandia Labs: Tool Development vs Operational Secrecy
Sandia National Laboratories’ Digital Assurance for High Consequence Systems (DAHCS) Mission Campaign builds tools for critical infrastructure protection but keeps its operations secret, which limits transparency. DAHCS wants to provide “empirical, ideally measurable digital assurance” for high consequence systems in nuclear weapons, hypersonics, space, and critical infrastructure missions. This partnership creates tension between tool development goals and security requirements. While tool development thrives on open collaboration, security needs restrict information sharing, which creates gaps in SCSP deployments.
SLTT Partnerships: Data Sharing Risks
State, Local, Tribal, and Territorial (SLTT) partnerships bring major data sharing risks. CISA’s SLTT Information Sharing Program aims to strengthen cyber defenses, but operational limits have pushed many organizations to use third-party products that alter shared content. All but one of these IOCs had no history on SLTT networks until recently, which made them safe to block without disrupting operations. Organizations still face CTI sharing infrastructure limits that cancel out the benefits of using community-accepted standards.
Vendor Lock-in and Update Delays in SCSP Latest Version
Heavy reliance on Symantec’s ecosystem creates vendor lock-in problems and makes integration with other solutions challenging. SCSP’s proprietary standards, unlike interoperable systems, limit migration options. Several critical vulnerabilities in SDCS:SA (SCSP’s predecessor) needed coordinated disclosure, but fixes took time—announced for December, moved to February, and released in mid-January. Current versions follow this same pattern, leaving systems exposed between vulnerability discovery and patching.
Conclusion
Symantec Critical System Protection looks like a resilient security solution for legacy systems and embedded devices, but serious vulnerabilities hide beneath its surface. Organizations using SCSP face real security risks even though it shows a clean vulnerability record since 2020. These risks come from several key areas that just need immediate attention.
Past vulnerabilities show a worrying pattern. Authentication bypass flaws, SQL injection vulnerabilities, directory traversal issues, and cross-site scripting weaknesses have affected SCSP versions of all sizes. Security teams should maintain careful patch management instead of assuming they’re protected.
Blind spots in cyber-physical security create major weak points. Failed network assessments, unsecured control systems, and poor up-to-the-minute monitoring leave critical infrastructure open to sophisticated attacks. SCSP doesn’t deal very well with emerging threats because it lacks AI-driven anomaly detection.
Tool limitations make these problems worse. SCSP’s forensic tools have reliability issues, and threat detection tools show limited scope. Mutually beneficial alliances with security organizations bring complex trade-offs between development goals and security needs.
SCSP’s kernel-level approach works better than application-level security to protect against day-zero attacks. But this needs deeper system integration and makes implementation more complex. Organizations should weigh these factors against their security needs.
Security professionals should look at Symantec Critical System Protection with clear eyes – seeing both its strengths and limits. Complete security means adding extra layers of protection to SCSP, especially for organizations running mission-critical infrastructure. Critical system protection needs an all-encompassing approach to fix the blind spots and vulnerabilities that SCSP can’t handle alone.
FAQs
1. What are hidden vulnerabilities in critical system protection?
Hidden vulnerabilities are weaknesses in security systems that are not immediately apparent but can be exploited by sophisticated attackers. These may include undocumented flaws in software, blind spots in monitoring, or limitations in threat detection capabilities.
2. How effective is kernel-level hardening compared to application-level security?
Kernel-level hardening, as used in Symantec Critical System Protection, provides stronger protection against day-zero attacks and offers broader system protection. However, it can be more complex to implement and may offer less granular control over specific program behaviors compared to application-level security.
3. What are some limitations of Symantec Critical System Protection for embedded devices?
SCSP faces challenges in protecting embedded devices, particularly in operational technology (OT) and industrial control system (ICS) networks. These systems prioritize availability and integrity over data confidentiality, which can conflict with traditional IT security approaches.
4. Are there any significant vulnerabilities in recent versions of Symantec Critical System Protection?
While SCSP has maintained a clean vulnerability record since 2020, earlier versions had critical vulnerabilities including authentication bypass, SQL injection, and cross-site scripting issues. It’s crucial for organizations to maintain up-to-date patch levels to address these potential security risks.
5. What are the main challenges in integrating cyber and physical security systems?
Key challenges include inadequate network assessments, unsecured control systems in critical deployments, and lack of real-time monitoring capabilities. The convergence of IT and OT systems has expanded the attack surface, creating new opportunities for sophisticated cyber attacks on physical infrastructure.

