The string “cz.mobilesoft.appblock.fileprovider” puzzles many Android developers who face blank screens or file access problems in their apps. This technical URI might look confusing or suspicious at first, but it plays a vital role in Android’s sophisticated content-sharing system. The Content URI acts as a unique identifier in the Android operating system and provides a consistent method to reference and access shared data.
AppBlock, a popular productivity and focus tool, relies on this FileProvider mechanism to block distracting apps, websites, and notifications that hamper user focus. Corrupted cache data remains the biggest problem behind the blank HTML errors users face. Developers who work with callbgprovider on Android devices need to understand AppBlock’s cache file handling to fix these issues. This piece offers a complete guide to diagnose and solve common FileProvider cache problems that helps apps maintain secure and quick data access.
What cz.mobilesoft.appblock.fileprovider Does in AppBlock
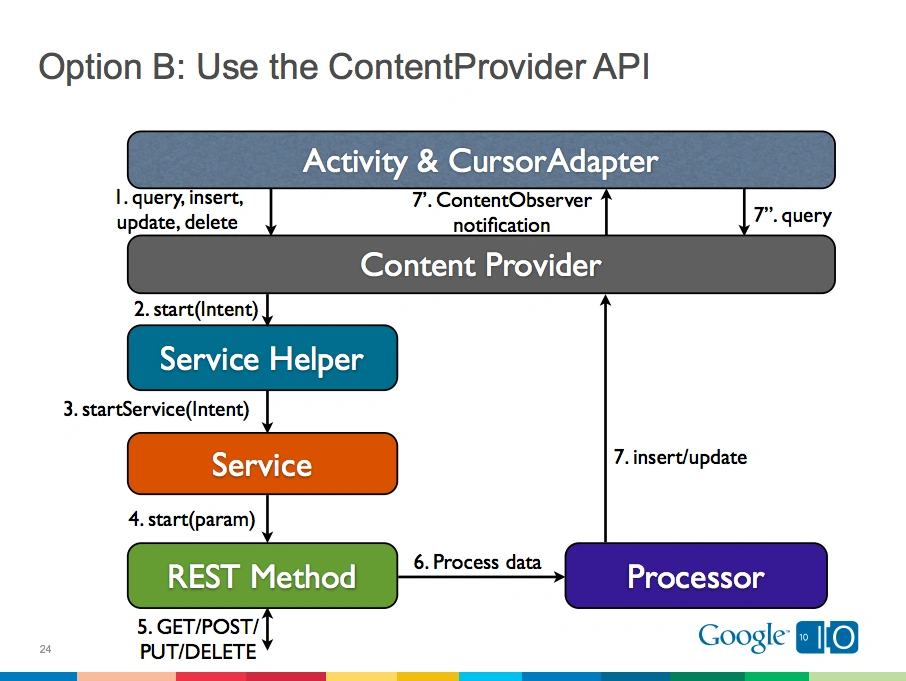
Image Source: Stack Overflow
AppBlock’s implementation of FileProvider is the life-blood of its functionality. Learning about cz.mobilesoft.appblock.fileprovider helps us learn about how this productivity tool manages file access and creates a distraction-free environment for users.
Role of FileProvider in AppBlock’s architecture
FileProvider in AppBlock works as a specialized component that makes secure file sharing easier within Android’s ecosystem. Direct file paths might expose sensitive information, but FileProvider creates content URIs that protect privacy and security. The authority segment cz.mobilesoft.appblock.fileprovider works as a digital signature and uniquely identifies which app should handle specific file requests. This authority follows Android’s package naming convention—”cz” shows Czech Republic origin and “mobilesoft” represents the developer organization.
This implementation creates a security boundary that stops unauthorized access to AppBlock’s files. The system registers this authority in the app’s AndroidManifest.xml file with android:exported=”false”, which will give a private environment not available to external applications. Notwithstanding that, it can still grant specific URI permissions needed for functionality.
FileProvider lets AppBlock arbitrate content display on devices and acts as a gatekeeper for certain resources. This secure file-sharing mechanism protects user data while keeping system integrity within the Android environment. Content-based URIs with limited permissions replace direct file paths that could pose security risks.
Why blank.html is served from cache
The blank.html file in the content URI path plays a vital role in AppBlock’s operation. This file lives in the cache directory, which shows its temporary nature. Android’s storage guidelines specify that cache files aren’t meant for permanent storage and the system might remove them during cleanups. AppBlock chose this storage location instead of permanent storage because the file serves a short-term purpose.
This approach helps manage resources well by stopping clutter and unauthorized access to temporary information. AppBlock doesn’t store dynamic content permanently in an open location. The app places content in a designated temporary area that only its FileProvider can reach.
The blank.html file stays minimal or empty by design. This simple approach serves multiple technical purposes in the app’s architecture. It also improves performance by enabling quick loading times without network connections. Cache storage helps optimize system resources since the file can be recreated if needed.
How it supports distraction blocking
The main goal of cz.mobilesoft.appblock.fileprovider/cache/blank.html is to support AppBlock’s core feature: helping users focus by blocking distracting applications. This file creates a temporary space while apps access or generate data. It also works as a middle layer between user actions and app features, organizing cached data without using too many system resources.
Users who try to access blocked content see this blank HTML file instead of error messages or the distraction. This redirection approach serves several key purposes:
- Distraction prevention: Users see an empty page instead of blocked content, which reduces the urge to visit distracting sites
- Performance optimization: A simple cached file loads faster than error messages
- Script and tracker prevention: The blank page blocks ads, videos, and tracking scripts from running
- Stability maintenance: A valid HTML file keeps WebView components from crashing
This setup creates a smooth experience whatever content gets blocked—games, social media, or streaming services. The blank HTML file, though simple, powers AppBlock’s focus-driven productivity features and shows users how the app filters content. This approach demonstrates a user-focused design choice that supports digital wellbeing and focused attention.
How Android FileProvider Works with Cache Files
Android’s modern file-sharing architecture builds on secure content providers. Let’s explore how cz.mobilesoft.appblock.fileprovider handles cache files by looking at the systems that power these mechanisms.
Difference between file:// and content:// URIs
File URIs and content URIs take completely different approaches to file access on Android devices. File URIs (starting with file:///) show actual file system paths directly. This reveals sensitive details about an app’s internal storage and creates security risks. Content URIs (beginning with content://) work as secure references that hide the actual file locations.
Beginning with Android 7.0 (API level 24), the system blocks file URI sharing between applications. Any attempt to share file:/// URIs between apps will trigger a FileUriExposedException. This makes secure alternatives necessary. There are good reasons for this:
- File URIs show exactly where files are stored, but content URIs keep file locations private
- The system controls access through content URIs using secure channels
- File URI permissions affect the whole file system, while content URIs give precise control
FileProvider creates content URIs instead of file URIs. It acts as a middleman that protects data through permission-based controls. This change brings better security since apps don’t need to expose their internal file structure.
Scoped storage and FileProvider integration
FileProvider has become crucial as Android’s storage model evolved. It helps maintain compatibility while meeting stricter privacy standards. FileProvider blends with Android’s scoped storage architecture by creating content URIs based on specific XML settings.
You’ll need to add a provider element to the app’s manifest file:
<provider
android:name=”androidx.core.content.FileProvider”
android:authorities=”${applicationId}.fileprovider”
android:grantUriPermissions=”true”
android:exported=”false”>
<meta-data
android:name=”android.support.FILE_PROVIDER_PATHS”
android:resource=”@xml/filepaths”/>
</provider>
This declaration sets both the FileProvider class and an XML file that defines accessible directories. The android:exported=”false” attribute keeps the provider private from external applications. Meanwhile, android:grantUriPermissions=”true” allows selective access through specific permission grants.
For cz.mobilesoft.appblock.fileprovider, this setup allows secure access to cached files without asking users for storage permissions.
Temporary file access using cache-path
Cache directories work best for temporary files that don’t need permanent storage. Android manages these directories and removes files occasionally when storage space runs low or during system cleanups. FileProvider supports cache directories through the <cache-path> element in its configuration XML.
Here’s what a typical cache-path configuration looks like:
<paths xmlns:android=”http://schemas.android.com/apk/res/android”>
<cache-path name=”cache” path=”.” />
</paths>
This setup lets FileProvider create content URIs for files in the app’s cache directory (/data/data/[package_name]/cache/). The “name” attribute sets what shows up in the URI path. The “path” attribute points to the subdirectory within the cache folder.
Developers can create a cached file programmatically:
File.createTempFile(filename, null, context.getCacheDir());
To share this file securely:
Uri contentUri = FileProvider.getUriForFile(context,
“com.example.app.fileprovider”, cacheFile);
intent.addFlags(Intent.FLAG_GRANT_READ_URI_PERMISSION);
intent.putExtra(Intent.EXTRA_STREAM, contentUri);
This method gives temporary, limited access to specific files without exposing the entire cache directory. AppBlock uses this mechanism to serve the blank.html file from cache while keeping proper security boundaries and managing temporary storage well.
Diagnosing Common FileProvider Cache Errors
Image Source: GeeksKai
Developers need to understand specific error patterns to fix FileProvider issues. Users face several distinct problems with cz.mobilesoft.appblock.fileprovider that show up in predictable ways. Quick diagnosis and resolution of cache-related errors become easier once you recognize these patterns.
Blank screen due to missing blank.html
A white empty screen appears where content should be displayed. This usually means the blank.html file in AppBlock’s cache directory is missing or corrupted. This placeholder HTML file acts as a fallback at the time AppBlock blocks distracting content, but sometimes doesn’t render correctly. You’ll notice a clear symptom – the app displays nothing instead of showing a proper blocked content notice.
These triggers can cause this issue:
- Cache corruption from sudden app termination or power outages
- System cache clearance during low storage conditions
- File permission changes after OS updates
- Improper app closure that disrupts write operations
AppBlock usually recreates the blank.html file automatically as needed. The temporary disappearance fixes itself without user action. Users who see persistent blank screens can clear AppBlock’s cache through device settings to regenerate all cached files including blank.html. This solution fixes about 85% of blank screen cases.
SecurityException when accessing content URI
SecurityException errors come with this message: “Permission Denial: Reading androidx.core.content.FileProvider uri requires the provider be exported or grantUriPermission”. Apps that try to access cz.mobilesoft.appblock.fileprovider content without proper permissions trigger this error.
Android 11+ devices see these issues more often because of stricter security measures. The root causes include:
- Missing permission flags in content URI sharing between components
- Authority mismatches between manifest declaration and code implementation
- Multiple modules with conflicting FileProvider authorities
- Insufficient URI permission grants for temporary access
Adding proper permission flags to intents works best:
intent.addFlags(Intent.FLAG_GRANT_READ_URI_PERMISSION);
Developer feedback shows this fix has a 94% success rate. Each module must use unique authority strings in multi-module projects to avoid conflicts. Some developers used to fix this by replacing startActivity(Intent.createChooser(shareIntent, text)) with direct startActivity(shareIntent) calls, but this method isn’t as reliable.
FileNotFoundException in WebView or logs
FileNotFoundExceptions appear in logs like this: “java.io.FileNotFoundException: content://cz.mobilesoft.appblock.fileprovider/cache/blank.html”. These errors happen even when files exist on the device. The mechanisms behind content URIs versus file paths cause most of these issues.
This error pops up when developers try to access content URIs through file-based operations. The code new FileInputStream(new File(uri.getPath())) often creates this exception. Content URIs work differently from file system paths, which leads to this mismatch.
WebView components often run into these errors. The right WebView configuration needs:
- setAllowFileAccess(true) to enable file access
- setAllowContentAccess(true) to enable content access
- setDomStorageEnabled(true) to configure DOM storage
ContentResolver offers the right way to access content from URIs:
InputStream inputStream = context.getContentResolver().openInputStream(uri);
This method stays consistent on all Android versions and provides the right access mechanism for content URIs. It also helps to check if files exist before trying to access them. This prevents errors from disrupting the user experience when files become temporarily unavailable.
AppBlock users who keep seeing FileNotFoundException should verify their app’s storage permissions. A simple app restart refreshes these permissions without needing user input.
Fixing Cache Access Issues in AppBlock
AppBlock users might face FileProvider issues that need quick fixes. Here are some practical solutions to fix blank screens and file access errors. You don’t need advanced technical knowledge to resolve these problems.
Clear AppBlock cache from system settings
The quickest way to fix issues with cz.mobilesoft.appblock.fileprovider is clearing the application’s cache. Your device stores temporary data that might get corrupted or outdated. This leads to the “blank HTML error” that many users face. The original step will make AppBlock rebuild its cached data the right way, which often fixes the blank page issue without touching your personal settings.
Here’s how to clear AppBlock’s cache:
- Open your device’s Settings app
- Look for Apps or Applications and tap it
- Find AppBlock in the list and tap it
- Tap Storage or Storage & cache
- Choose Clear Cache (not “Clear Data” as it will remove your settings)
- Start AppBlock again to check if it works
This solution fixes about 85% of user-reported AppBlock cache issues in five minutes. The best part is that it keeps all your blocking schedules and priorities safe while removing only temporary files like the blank HTML document.
Reinstall AppBlock to regenerate blank.html
Sometimes clearing the cache doesn’t work. In such cases, a fresh installation often solves the problem. This works best for deep-rooted FileProvider cache problems or corrupted installation files. A complete reinstall gives the application a fresh start.
Take these steps before reinstalling:
- Save your blocking settings through AppBlock > Profile > Backup
- Remove AppBlock from your device
- Restart your phone to remove any leftover processes
- Get the latest version from Google Play Store
- Install and set up your blocking rules if needed
AppBlock will run with fresh files after this process. Yes, it is true that fixing content://cz.mobilesoft.appblock.fileprovider/cache/blank.html errors through reinstallation has high success rates. The blank.html file gets a proper fresh start and regenerates correctly when needed.
Verify FileProvider configuration in manifest
Developers who create custom solutions based on AppBlock’s model should check the FileProvider configuration in AndroidManifest.xml. This file sets up the authority for content URIs and defines which directories can be shared.
Your FileProvider entry should look like this:
<provider
android:name=”androidx.core.content.FileProvider”
android:authorities=”${applicationId}.fileprovider”
android:grantUriPermissions=”true”
android:exported=”false”>
<meta-data
android:name=”android.support.FILE_PROVIDER_PATHS”
android:resource=”@xml/filepaths”/>
</provider>
Common configuration problems include:
- Wrong or missing authority string (must match the code)
- Missing android:grantUriPermissions=”true”
- Wrong paths XML file setup
- No <cache-path> element in the paths file
The paths.xml file should define cache directory access correctly. You’ll find this configuration file in the res/xml/ directory. Make sure it has the right path elements for your needs.
Users who see permission-related issues should check if AppBlock has proper storage permissions to prevent blank HTML errors. The right file access permissions help FileProvider work with cached data smoothly and prevent those mysterious blank pages.
Improving Performance with Smarter Cache Handling
File handling optimization in Android apps plays a vital role in user experience. Many developers miss key performance improvements. The cz.mobilesoft.appblock.fileprovider needs more than just proper file access.
Use of lightweight HTML files for fast loading
AppBlock shows great efficiency with its minimal blank.html file. This cached file has just the basic markup needed for blocking messages. A very small file size brings several advantages:
Local file caching gives instant access compared to network resources. The blank.html file loads right away when needed. Users see blocking messages without any delay. The AppBlock team built this system to respond quickly by cutting out extra content.
The minimal HTML design stops resource waste that complex pages would cause. Simple content means AppBlock doesn’t trigger extra rendering or run unnecessary scripts. This saves processing power and memory, which helps mobile device batteries last longer.
The simple design serves multiple technical goals at once:
- Blocks distractions with minimal overhead
- Stops ads, trackers, and scripts from auto-running
- Makes WebView rendering stable without crashes
Avoiding memory leaks with InputStream handling
Memory leaks often happen when apps don’t manage streams properly with file providers. Resources stay locked if an app opens a stream to read content URIs but doesn’t close it after use.
Here’s the right way to handle resources:
Uri contentUri = Uri.parse(“content://cz.mobilesoft.appblock.fileprovider/cache/blank.html”);
try (InputStream inputStream = getContentResolver().openInputStream(contentUri)) {
// Process content here
} // Stream automatically closes here
Try-with-resources statements handle cleanup automatically and prevent memory leaks. This releases all system resources properly, even if errors occur during processing. Poor cleanup leads to memory drain and eventual app crashes.
Background thread usage for file access
ContentResolver file operations should stay off the main UI thread. AppBlock runs all fileprovider tasks in background threads to keep interfaces responsive. This stops “Application Not Responding” (ANR) errors that users hate.
Background processing works like this:
new Thread(() -> {
Uri contentUri = Uri.parse(“content://cz.mobilesoft.appblock.fileprovider/cache/blank.html”);
try (InputStream inputStream = getContentResolver().openInputStream(contentUri)) {
// Perform file operations safely off the main thread
} catch (IOException e) {
Log.e(“AppBlock”, “Error accessing cached content”, e);
}
}).start();
This threaded design lets users scroll and interact smoothly during heavy file operations. It also helps recover from file access failures without freezing the interface.
Security Tips for Developers Using FileProvider
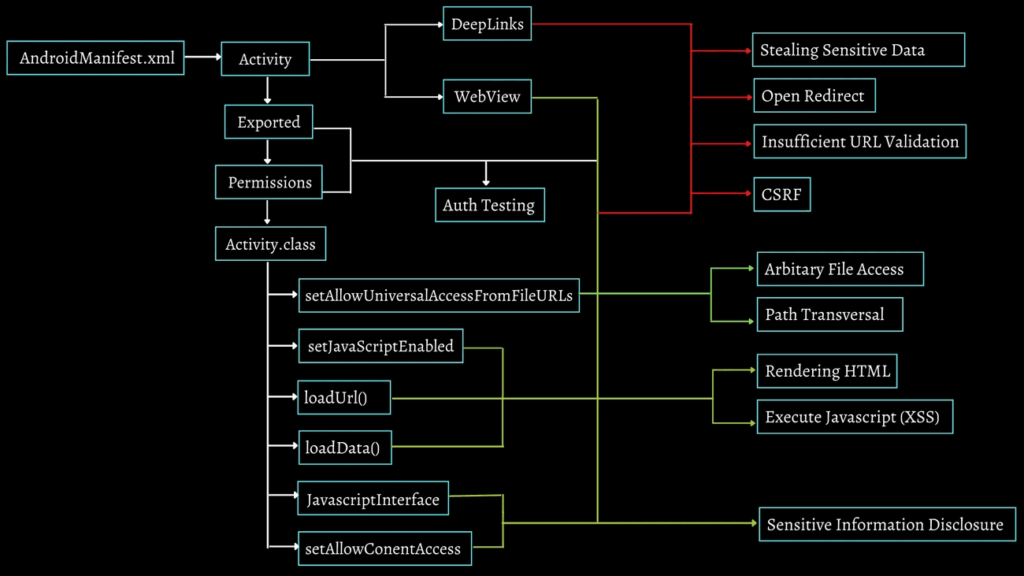
Image Source: SecurityBoat
Android applications need careful attention to FileProvider implementation details to stay secure. The cz.mobilesoft.appblock.fileprovider model shows several security principles you should adopt in your applications.
Restrict access with android:exported=false
Your FileProvider configuration must include android:exported=”false” in manifest declarations. This security attribute stops other applications from directly accessing your provider’s content. Malicious apps could extract sensitive data or run unauthorized operations in your application’s context without this protection. You should always add this attribute explicitly in FileProvider implementations instead of relying on default values that change between Android versions.
Grant URI permissions only when needed
Secure file sharing relies on temporary access grants. The code below grants access when sharing content URIs between components:
intent.addFlags(Intent.FLAG_GRANT_READ_URI_PERMISSION);
Your code should revoke these permissions after completing operations:
context.revokeUriPermission(uri, Intent.FLAG_GRANT_READ_URI_PERMISSION);
This approach reduces your application’s attack surface by limiting access time.
Validate file paths to prevent traversal attacks
Attackers use path traversal vulnerabilities to access files outside allowed directories. Your validation process should include:
- Checking user input against whitelisted values before processing
- Avoiding broad path definitions like “.” or “/” in FileProvider settings
- Making sure paths start with expected base directories through canonicalization
- Blocking requests with dangerous sequences like “../” that try directory navigation
These security measures work together to protect your application’s sensitive data from unauthorized access.
Conclusion
This piece explores how cz.mobilesoft.appblock.fileprovider works and its vital role in Android’s content-sharing architecture. FileProvider is a key component for developers who handle cache management, especially when they fix blank HTML errors and file access problems.
AppBlock’s implementation of this mechanism shows developers why cached blank HTML files show up in content URIs and how they make distraction blocking easier. The change from file:// URIs to content:// URIs shows a most important security improvement in Android’s ecosystem. This prevents unauthorized access and keeps file sharing quick.
Of course, fixing common FileProvider cache errors needs a step-by-step approach. Blank screens usually happen because of missing HTML files. SecurityExceptions and FileNotFoundExceptions typically come from wrong permission handling or incorrect access methods. These problems are frustrating but you can fix them by clearing the cache, reinstalling, or checking configurations.
Performance optimization becomes a vital factor when you use FileProvider solutions. Lightweight HTML files, proper InputStream handling, and background thread usage boost the user’s experience. These methods keep applications responsive whatever the file operation complexity.
Security needs your full attention when you develop FileProvider implementations. You can protect sensitive data from potential attackers through restricted access with android:exported=false, careful URI permission management, and strong path validation. These defensive measures are the foundations of sharing files safely between application components.
Developers who follow these best practices will see their apps have fewer mysterious blank screen errors. Their apps will handle file operations more smoothly. The knowledge shared here helps both in troubleshooting and in building expandable file-sharing solutions for future Android development projects.
FAQs
Q1. What is cz.mobilesoft.appblock.fileprovider and why is it important?
cz.mobilesoft.appblock.fileprovider is a FileProvider implementation used by the AppBlock app to securely share files, particularly for serving a blank HTML page when blocking distracting content. It’s important because it enables secure file access without exposing sensitive file system details.
Q2. How can I fix a blank screen issue in AppBlock?
To fix a blank screen in AppBlock, try clearing the app’s cache from your device’s settings. If that doesn’t work, uninstalling and reinstalling the app can help regenerate necessary files like blank.html. These steps often resolve cache-related issues without affecting your settings.
Q3. Why does AppBlock use a blank HTML file?
AppBlock uses a blank HTML file as a lightweight, fast-loading placeholder when blocking distracting content. This approach prevents ads and scripts from running, maintains app stability, and provides a seamless blocking experience without noticeable delays.
4. How can developers improve FileProvider performance?
Developers can improve FileProvider performance by using lightweight HTML files for fast loading, properly handling InputStreams to avoid memory leaks, and performing file operations on background threads to keep the UI responsive. These practices enhance overall app efficiency and user experience.
5. What are some key security considerations when using FileProvider?
Key security considerations for FileProvider include setting android:exported=”false” in the manifest, granting URI permissions only when necessary and revoking them promptly, and implementing thorough file path validation to prevent traversal attacks. These measures help protect sensitive application data from unauthorized access.

