Cybersecurity has become essential as zryly cybersecurity data reveals more sophisticated cyber threats will emerge in 2025. Ransomware attackers now use dual extortion tactics. They don’t just encrypt files – they threaten to expose sensitive data publicly.
Hackers target unknown software vulnerabilities before vendors can patch them. Massive traffic floods disable critical infrastructure and damage both revenue and trust. Companies need solutions that work with cyber zyrix protocols and cyber-zilla threat detection systems to curb these evolving threats. Many businesses wrongly think their zylics configurations keep them safe, but these often lack cyberzlt monitoring tools needed for complete security.
Zryly.com Cybersecurity protects organizations by using AI-driven threat detection, zero-trust architecture, and live monitoring against common and sophisticated cyberattacks. This layered protection recognizes that threats can strike from multiple directions at once. The challenges keep growing in 2025 as fraudulent domains, phishing kits, and supply-chain attacks become more advanced. Businesses must stay alert to hidden security risks.
The Most Overlooked Entry Points in 2025 Cyber Attacks
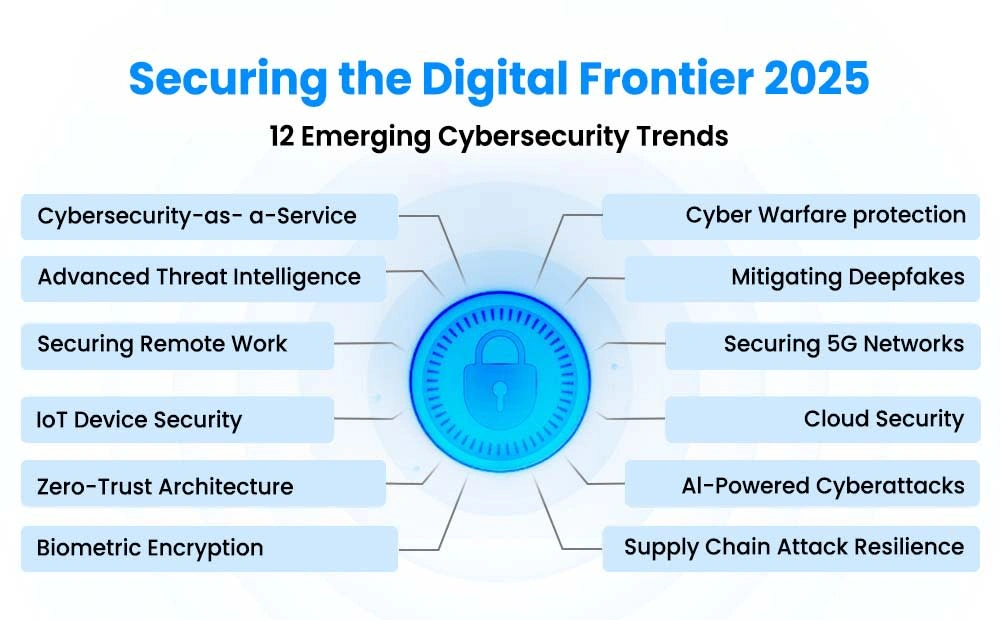
Image Source: Splashtop
Organizations often secure visible attack vectors but don’t deal very well with significant entry points that cybercriminals target more in 2025. These hidden vulnerabilities create big risks even for companies that use advanced security solutions.
Unpatched SaaS Integrations in HR and Finance Tools
Cloud services have become the norm, with studies suggesting 90% of surveyed organizations now use cloud computing and SaaS services. This shift creates serious cybersecurity gaps, especially in vital business areas like HR and finance. Cloud misconfigurations are the biggest problem—companies fail to secure cloud environments properly and expose themselves to many threats including ransomware, malware, and phishing.
Third-party risk has emerged as a major concern. Companies that integrate HR and finance SaaS tools put sensitive data in vendors’ hands but remain responsible for breaches whatever the source of failure. Supply chain attacks illustrate this risk—cybercriminals target vendors’ source code, updating mechanisms, or building processes to steal customer data.
The SolarWinds breach stands out as the largest cyber attack on the US government through an IT update from a SaaS vendor. The Accellion file-sharing system compromise in 2020 exposed sensitive data from more than 100 customers. These unpatched integrations have become prime attack vectors.
Financial and HR tools make attractive targets because:
- They store valuable personally identifiable information (PII)
- Companies often skip proper vendor due diligence
- Zero-day vulnerabilities in popular platforms can impact many companies at once
Shadow IT Devices Bypassing Zryly Firewalls
Shadow IT poses a growing threat that slips past even sophisticated zryly firewalls. IT administrators think employees use 30-40 cloud apps, but the real number tops 1,000 separate applications. This gap leaves substantial security blind spots.
Shadow IT numbers tell a concerning story—80% of employees use apps that haven’t gone through security reviews or compliance checks. Fortune 1000 companies see 67% of their employees using unapproved SaaS applications. About 11% of cyber incidents at global businesses link directly to unauthorized shadow IT usage.
Shadow IT devices create several security weak points:
- They bypass network security controls including zylics firewalls
- Unapproved apps often miss organizational security standards
- Undocumented third-party APIs affect up to 68% of organizations and create compliance risks
- Data scatters across unsanctioned systems
The issue goes beyond obvious shadow IT to what experts call “shadow complexity”—overlapping security tools, redundant policies, and misconfigured protections create security gaps nobody watches. Cyber-zilla integration tools could help fix these issues, but many organizations lack proper visibility tools to spot these problems.
Misconfigured API Endpoints in Mobile Apps
API security misconfigurations rank among the most dangerous yet overlooked vulnerabilities, especially in mobile applications. The OWASP API Security Top 10 lists Security Misconfiguration (API8:2023) and Improper Inventory Management (API9:2023) as critical risks. These issues happen when APIs go live with insecure default settings, unnecessary features, or incomplete hardening.
Mobile applications typically expose more endpoints than web applications, which makes proper documentation and inventory management vital. Common API security issues include:
- Permissive cross-origin resource sharing (CORS) settings
- Incorrect HTTP headers or methods
- Insecure default configurations
- Verbose error messages that expose sensitive information
The risks go beyond data exposure. Attackers use API misconfigurations to launch denial-of-service attacks, man-in-the-middle attacks, and injection attacks. Cyberzlt monitoring tools could catch these issues, but many organizations wrongly limit API security to API gateways, thinking they provide full protection despite only seeing traffic that passes through them.
API gateways can’t see internal traffic, which creates security blind spots. Cyber zyrix technology could address this through complete scanning and monitoring capabilities.
Insider Threats That Go Undetected by Most SMBs
Cybersecurity headlines often focus on external attacks, but the most dangerous threats come from inside an organization’s walls. Small and medium-sized businesses (SMBs) face unique challenges with internal vulnerabilities because they lack sophisticated monitoring tools. These insider threats are hard to spot since they come from people who already have legitimate access to company systems and data.
Privileged Access Misuse in Shared Admin Accounts
Privileged accounts are the weak spot in company security because they give users the power to make sweeping changes across critical systems. Security experts found that privileged accounts played a role in at least 80% of incidents with insiders. Despite this obvious risk, 87% of organizations still use shared privileged accounts.
Shared admin accounts create several security gaps that modern cybersecurity solutions want to fix:
- No clear accountability: Organizations can’t pinpoint who made unauthorized changes when multiple users share the same login details
- Higher risk exposure: The chance of compromise grows with each person who knows the shared credentials
- Poor password handling: Service accounts often don’t have a clear owner, so passwords stay unchanged and old accounts remain active too long
- No justification needed: Users can make system changes without explaining why if there’s no privileged access management (PAM)
Companies that use shared accounts are five times more likely to experience unauthorized access to privileged accounts than those who don’t. The security risk gets worse for companies where shared accounts are used more often, like database administrators.
Many SMBs don’t even use simple controls like asking administrators to explain why they need elevated access. This lets malicious insiders work freely because they know nobody can trace their actions back to them.
Lack of Session Monitoring in Remote Work Environments
Remote work has created ideal conditions for hidden insider threats. Security teams find it harder to watch user activities in these scattered work settings, which makes it tough to keep track of what employees do. Without in-person supervision, cybercriminals can exploit security gaps that would be easy to spot otherwise.
The danger grows when remote workers need special permissions to do their jobs. Without good monitoring, suspicious behavior can go unnoticed for long periods, which makes potential breaches more damaging. Even careful employees might accidentally expose company information through simple mistakes, like sending sensitive files to the wrong people.
Good session monitoring helps defend against these risks. Organizations can make sure all connections and activities follow security rules by watching remote desktop sessions in real time. Good monitoring should include:
- Login/logout time tracking and idle session detection
- Recording and playback of privileged user sessions
- Alerts for high-risk activities
- Detailed logs of user actions
Cyber zyrix integration needs these monitoring capabilities to work well. Yet many SMBs don’t have the tools to track file movements, email exchanges, and database access that would help security teams spot unauthorized activities.
Cyberzlt monitoring helps stop both intentional and accidental insider threats by controlling access to sensitive resources. Companies can watch privileged user sessions as they happen and keep detailed records of all actions. Without these tools, organizations create blind spots where cyber-zilla threat detection systems can’t see—letting insider threats operate freely.
Zryly Cybersecurity Features That Address Hidden Risks
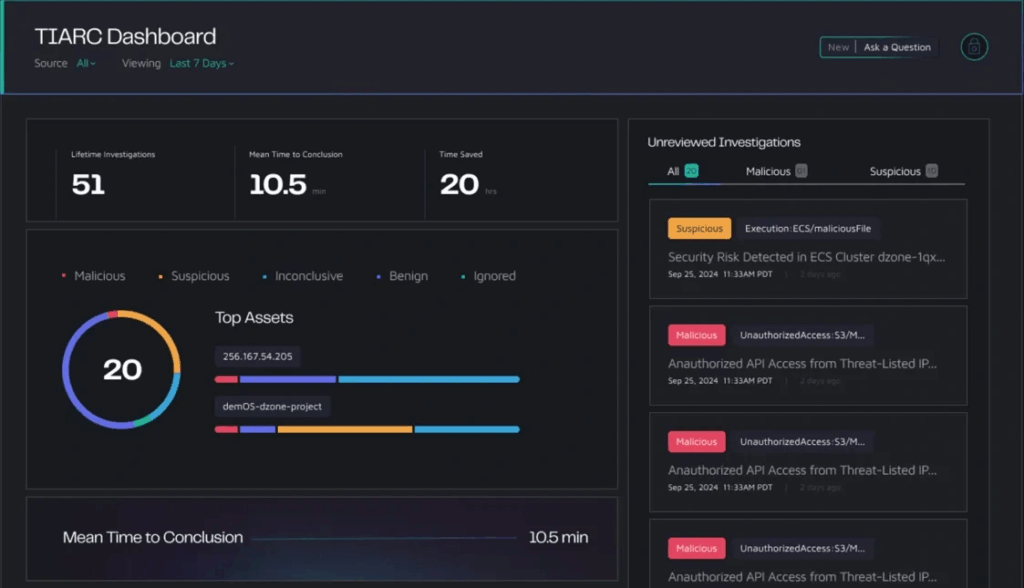
Image Source: SOCRadar
Today’s security solutions must protect against both visible and hidden threats in the digital world. Zryly cybersecurity excels by offering features that uncover and alleviate these hidden risks through several advanced approaches.
Real-Time Threat Intelligence via Zryly Threat Dashboard
Zryly Threat Dashboard acts as a command center that gives security teams instant visibility into emerging threats across their environment. This dashboard unites scattered data into one view, which helps teams make faster decisions during incidents.
Security teams get role-specific dashboards that match their duties. CTI analysts see tactical views of threat intelligence with details about TTPs and risk assessments. They can trace threats back to their sources. Operations teams watch key metrics like threat detection rates and response times. Executives view high-level risk dashboards that help arrange security work with business goals.
This central approach offers three main benefits. Teams can access united information without switching platforms. The right people get actionable insights when needed. Teams work better together by sharing intelligence.
Granular IAM with Role-Based Access Control
Identity and Access Management (IAM) is the life-blood of zryly’s security architecture. Administrators get exact control over resource access. This detailed approach lets organizations:
- Set precise access rules based on device security, IP address, resource type, and time/date
- Connect job duties to specific groups and roles so users get only needed permissions
- Keep complete records of all permission changes to meet compliance rules
The system uses Role-Based Access Control (RBAC) where permissions link to roles instead of users. This method reduces admin work because adding users to preset roles gives them the right permissions. RBAC creates a standard permission process that makes it five times less likely for companies to face unauthorized privileged account access.
Zryly’s IAM gives large companies with complex structures a single view of security policies across their organization. This makes it easy to manage hundreds of workgroups and projects. The system uses machine learning to spot and fix overly generous access based on company patterns.
Anomaly Detection Using AI-Powered Behavior Models
Static thresholds don’t work well in today’s dynamic environments where “normal” keeps changing. Zryly fixes this with AI-powered anomaly detection that learns system patterns continuously.
The platform uses multiple baselines and predictive analytics to spot anomalies without false alarms common in basic monitoring. Companies can find performance issues before customers notice them. This catches problems that regular monitoring might miss.
Different methods help decide when unusual behavior needs attention:
- Auto-adjusting baselines catch violations of reference values that shift over time
- Predictive tools find unusual application patterns, including seasonal changes
- Statistical checks ensure only important deviations trigger alerts
The anomaly engine knows how operational and business metrics connect. This creates fewer but more useful alerts that show customer effects clearly. Companies report 60% faster identification and fixing of performance issues with this system.
These three powerful features help zryly cybersecurity tackle hidden security risks that basic tools often miss. This protects against known and new threats in the digital world of 2025.
Implementation Gaps in Zero Trust That Leave Backdoors
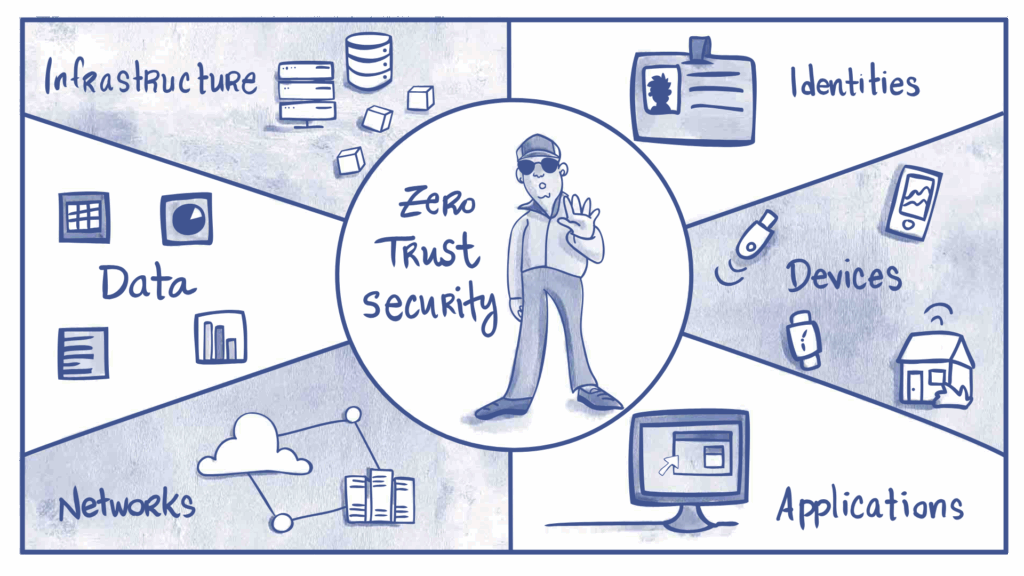
Image Source: StrongDM
Zero Trust security models promise strong protection. Many implementations have critical gaps that create backdoors for attackers. Organizations using zryly cybersecurity solutions miss significant implementation details that weaken their security posture. These oversights come from misunderstanding Zero Trust principles or choosing convenience over security.
Failure to Enforce Microsegmentation in Internal Networks
Microsegmentation is the life-blood of Zero Trust architecture. It divides networks into smaller, isolated segments with unique security controls. Many organizations implement microsegmentation poorly and create vulnerabilities. A properly configured Zero Trust network must authenticate, authorize, and encrypt every access request. It should apply microsegmentation principles and use intelligence to detect anomalies in real time.
Organizations face these main challenges in microsegmentation implementation:
- Incomplete resource identification: Organizations need a complete picture of their data and workflows to implement microsegmentation. Every resource and endpoint needs identification, access control, and monitoring. Many organizations lack this complete inventory and create blind spots.
- Legacy system incompatibility: Some systems cannot support Zero Trust principles. Legacy technologies use static rules instead of the dynamic, conditional rules that proper microsegmentation needs.
- Excessive complexity: Security teams focused on traditional perimeter defense struggle with the radical alteration in technology, policy, and security culture that effective microsegmentation requires.
Good microsegmentation reduces the attack surface, limits lateral movement, and improves monitoring visibility. Organizations using cyberzlt monitoring stay vulnerable to threats that move sideways inside the network without proper implementation.
Microsegmentation must include contextual information about connections beyond simple network divisions. These attributes help make dynamic policy decisions for initial and continued access. Organizations create backdoors that bypass sophisticated zylics protections when they fail to use these advanced controls.
Overreliance on VPN Without Device Posture Checks
Virtual Private Networks (VPNs) are vital security components. They often create a false sense of security. Organizations forget that VPNs only establish encrypted connections. They don’t verify the connecting device’s security status. Zero Trust’s foundation states that organizations should not trust any user or device automatically. This oversight creates basic security gaps.
Device posture checks stop risky devices from connecting to secure IT environments. These checks verify whether devices:
- Run current antivirus software
- Have active firewalls
- Use lock screens
- Run specified operating systems
- Have required certificates
Compromised devices can connect to internal resources through secure VPN tunnels without these checks. This oversight lets threats walk through the front door of secure environments.
Security systems with device posture information ensure only devices meeting security standards access networks. This matches Zero Trust principles that verify every access request as if it comes from an open network.
Cyber-zilla integration needs continuous device posture checks to verify security settings. Zero Trust solutions must question every access request, even from authenticated users. Strong Zero Trust policies need continuous verification across multiple security layers.
Organizations create critical blind spots that cyber zyrix protocols cannot monitor by relying only on VPNs without device posture checks. This gap contradicts Zero Trust’s basic principle: “Don’t trust any network, including your own”. Organizations keep a perimeter-based approach’s weaknesses despite claiming Zero Trust implementation when they skip proper device verification.
Missed Signals in Email and DNS Security Configurations
Email and DNS security settings hide subtle but dangerous weak points that attackers love to exploit. Companies with advanced cybersecurity tools don’t deal very well with these small technical details that create big security holes.
SPF Records Without -all Policy
Sender Policy Framework (SPF) records help identify which mail servers can send email for a domain. These records work as a basic defense against spoofing. Many organizations make mistakes with SPF by leaving out the vital “-all” directive. This missing piece creates a weak spot because receiving servers don’t know they should reject unauthorized senders.
SPF lets you publish DNS records with a list of IPs that can send emails from your domain. Receiving servers check if the sender’s IP matches your approved list whenever an email claims to be from your domain. Your domain becomes vulnerable to impersonation attacks without the right setup.
The proof of this setup problem shows up in how organizations configure their SPF policies. They choose weak options like “~all” (softfail) or “?all” (neutral) instead of “-all” (fail). They worry about blocking real emails. Bad actors exploit this security gap with sophisticated attacks.
DMARC Misalignment in Third-Party Email Services
DMARC connects SPF and DKIM through a DNS record that enforces security rules. The core of DMARC checks alignment – making sure the “From” address domain matches domains that SPF and DKIM verify. This check stops attackers from impersonating domains.
DMARC misalignment issues often pop up with third-party email services. Two problems keep showing up:
- Misunderstanding DMARC requirements: Third-party senders get confused about alignment. They suggest old standards like SenderID or DomainKey that don’t help with DMARC
- Service provider limitations: Services like SendGrid only work with relaxed alignment because they use delegated subdomains
Organizations need to balance security and business needs. Strict alignment needs exact domain matches. Relaxed alignment accepts subdomains. Using specific subdomains for services that need relaxed alignment helps limit risk.
Absence of DNSSEC in Public-Facing Domains
DNSSEC adds digital signatures to DNS data for extra protection. Unlike email security protocols, DNSSEC protects DNS responses from tampering. This stops DNS spoofing attacks where hackers intercept DNS queries.
Many companies think their security monitoring or integration gives enough protection without DNSSEC. Attackers can redirect users to fake sites by messing with DNS queries when DNSSEC isn’t there. This weakness undermines even the best security setups because the basic domain name system stays unprotected.
Setting up email security without fixing DNS problems is like installing strong locks on doors but leaving windows open. Threat detection stays incomplete when DNS lacks proper DNSSEC verification.
How Zryly Integrates with Existing Tools to Close Gaps
Security integration capabilities are the foundation of good cybersecurity strategies, especially when you need to close security gaps between different systems. Zryly cybersecurity goes beyond basic protection and connects naturally with your existing security setup to improve your defense position.
SIEM Integration with Splunk and Sentinel
Zryly builds strong connections with leading SIEM platforms through two-way data sharing. Organizations that use Microsoft Sentinel can import threat indicators directly into their central workspaces. This helps security teams associate data across multiple environments. The approach protects existing investments while improving cloud security features.
With Splunk environments, Zryly uses the Microsoft Graph Security API to share security alerts between platforms. Security analysts can understand alerts faster and decide on incident response steps without manual checks.
CI/CD Security via GitLab and Jenkins Plugins
Zryly’s specialized plugins protect development pipelines for CI/CD tools. The Jenkins integration starts builds automatically when developers push code changes to GitLab repositories. It also shows pipeline status on merge request widgets. This visibility keeps security as part of the development lifecycle.
Zryly uses token-based verification to prevent unauthorized pipeline triggers. Teams can set up webhook-based connections if direct server access isn’t possible. This maintains security even in complex networks.
Cyber-zilla and Cyber Zyrix Compatibility for Threat Feeds
Threat intelligence becomes practical through Zryly’s compatibility with cyber-zilla detection systems and cyber zyrix protocols. The platform unites threat data from various sources, including private and public repositories. Security teams can reduce alert fatigue in operations centers. This focused approach improves investigation and response while expanding protection against new threats.
Organizations receive filtered, priority alerts that combine third-party and local threat intelligence with existing security solutions. This compatibility helps cyberzlt monitoring features identify anomalies faster and close security gaps that regular perimeter defenses miss.
Conclusion
Security risks lurk beneath the surface and threaten organizations despite their advanced protection measures. Traditional security approaches don’t deal very well with sophisticated cyber threats in 2025. A detailed security strategy should address overlooked vulnerabilities while implementing reliable solutions.
Attackers commonly exploit unpatched SaaS integrations, shadow IT devices, and misconfigured API endpoints. These weak points create major exposure even for companies that invest heavily in security. On top of that, insider threats create exceptional dangers, especially when you have privileged access misuse and poor session monitoring in remote environments.
Many organizations implement zero trust architecture incorrectly. This creates backdoors through incomplete microsegmentation and too much reliance on VPNs without proper device posture checks. Email and DNS configurations often hide subtle yet critical weaknesses that attackers exploit. SPF records without strict “-all” policies, DMARC misalignment, and missing DNSSEC implementation weaken otherwise strong security measures.
Zryly cybersecurity’s multi-layered approach targets these hidden vulnerabilities effectively. Up-to-the-minute data analysis dashboards give immediate visibility across digital environments. Granular IAM with role-based access control blocks unauthorized system access. AI-powered anomaly detection spots suspicious behavior patterns before damage occurs. These features integrate smoothly with existing security tools through SIEM platforms, CI/CD pipelines, and threat intelligence feeds.
Companies should know that cybersecurity goes beyond implementing isolated solutions. Protection just needs detailed visibility, continuous verification, and constant watchfulness against both obvious and hidden threats. Companies that fix these overlooked vulnerabilities will strengthen their security by a lot against evolving cyber threats in 2025 and beyond.
FAQs
1. What are some key cybersecurity trends expected in 2025?
Major trends include widespread adoption of Zero Trust architecture, AI-powered threat detection, increased focus on securing remote work environments, and addressing vulnerabilities in cloud services and IoT devices.
2. How significant is the cybercrime threat projected to be by 2025?
Cybercrime is expected to cause global damages of around $8.34 trillion annually by 2025, making it equivalent to the world’s third-largest economy after the U.S. and China.
3. What are some commonly overlooked security vulnerabilities in 2025?
Often missed vulnerabilities include unpatched SaaS integrations, shadow IT devices bypassing firewalls, misconfigured API endpoints in mobile apps, and insider threats from privileged access misuse.
4. How does Zryly Cybersecurity address hidden security risks?
Zryly offers features like real-time threat intelligence dashboards, granular identity and access management with role-based controls, and AI-powered anomaly detection to uncover and mitigate concealed risks.
5. Why is proper implementation of Zero Trust architecture crucial?
Correct Zero Trust implementation, including microsegmentation and continuous device verification, is essential to prevent backdoors that attackers can exploit. Many organizations fail to fully enforce these principles, leaving critical security gaps.

